They Do Not Begin By Asking for Secrets: How Intelligence Recruitment Actually Works
 Aether-Intel6 min read·Just now
Aether-Intel6 min read·Just now--
Foreign intelligence recruitment has moved online.
The tradecraft that once required physical meetings in third countries, dead drops, and elaborate cover arrangements now operates primarily through LinkedIn connection requests, dark web forum rapport-building, and Telegram conversations that begin with apparent professional interest and end, months later, with a request that crosses a legal and ethical line.
The digital environment hasn’t changed the fundamental psychology of human recruitment. It’s dramatically lowered the cost of identifying targets, initiating contact, and maintaining the long-term relationship development that professional recruiters call “cultivation.”
Here’s what I’ve learned from nearly two decades of observation:
Professional recruiters, whether state-sponsored or non-state, almost never begin with a request.
They begin with recognition.
The target receives something they didn’t know they needed: to be seen, to be valued, to be understood by someone who appears to know their field and appreciate their contributions.
This emotional investment is the operational asset.
The request, when it comes, arrives after trust has been established, after reciprocity has been accumulated, after the target has already provided enough that refusal feels disproportionate to what’s being asked.
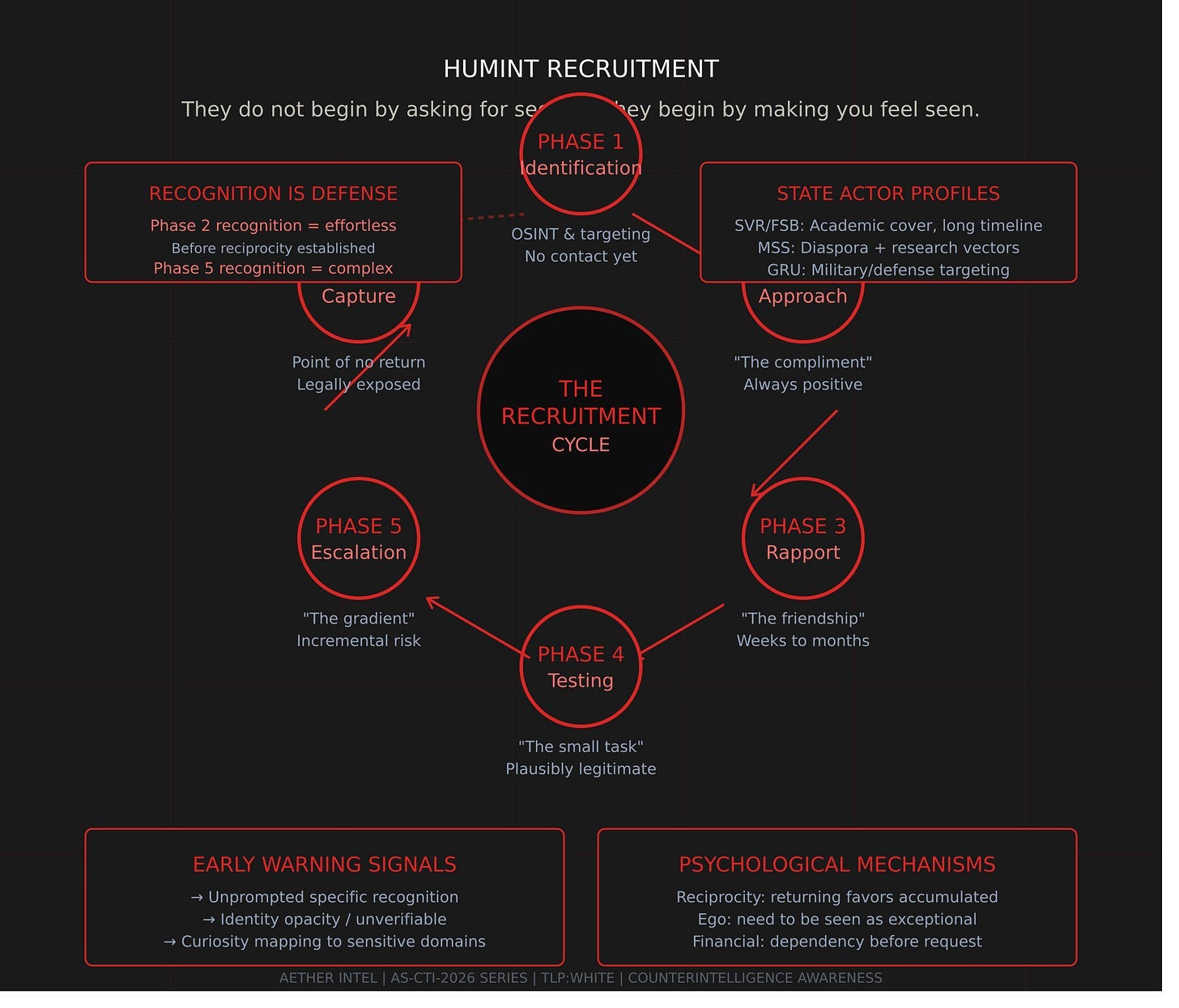
The Universal Pattern — The Recruitment Cycle:
I’m about to describe a pattern I’ve watched operate on dark web forums across different platforms, different languages, different target demographics, and different recruiting organizations. The specific details change. The psychological sequence does not.
Phase 1: Identification & Targeting
- Recruiter identifies candidate via OSINT or community monitoring
- Candidate has: access, exploitable profile, reachability
- No contact yet. Candidate is unaware.
Phase 2: Approach — “The Compliment”
- First contact is always positive. Never a request.
- “I read your post/paper/comment. Very insightful.”
- “You clearly understand X better than most people here.”
- PURPOSE: Activate ego. Make target feel seen by someone credible.
Phase 3: Rapport Building — “The Friendship”
- Regular, low-demand contact. Professional discussion.
- Recruiter demonstrates knowledge and interest in target’s field.
- Small reciprocal exchanges: ideas, information, recommendations.
- Duration: weeks to months. No request yet.
Phase 4: Testing — “The Small Task”
- First request: small, plausibly legitimate, easy to fulfill.
- “Can you clarify something about X for me?”
- “Do you have a contact at Y organization?”
- If target complies: relationship deepened, reciprocity activated.
Phase 5: Escalation — “The Gradient”
- Requests increase in sensitivity and risk incrementally.
- Each step feels small relative to the one before.
- Target is now invested — refusing feels like betraying the relationship.
- Financial elements may be introduced.
Phase 6: Capture — “The Point of No Return”
- Target has provided enough to be legally exposed.
- Relationship maintained by: loyalty, financial dependency, coercion leverage.
- Exit becomes psychologically and legally complex.
The most consistent observation:
The universality of the compliment phase.
Recruiters who would never identify themselves as such — who maintain every plausible cover from academic researcher to industry consultant to fellow community member — all open with recognition.
It’s not charm. It’s technique.
The target who is recognized as uniquely capable, uniquely knowledgeable, uniquely interesting is a target who has already begun to invest emotionally in the relationship before any request is made.
The compliment is not the beginning of a conversation. It’s the beginning of an operation.
State Actor Profiles:
Different intelligence services recruit differently, but the core pattern persists:
SVR/FSB (Russia): Long-timeline cultivation through academic and professional cover. Patience is the distinguishing characteristic — 12–24 month cultivation timelines before any sensitive request. The investment is proportional to target value.
MSS (China): Two tracks — diaspora targeting (cultural obligation framing, family pressure) and research targeting (academic collaboration, conference invitations). WeChat ecosystem provides communication access that Western CI can’t monitor with equivalent ease.
GRU (Russia): Military and defense community targeting. More willing to use direct financial offers at earlier stages when targets with confirmed access are identified.
North Korea: Transactional model for financial crime. Technical job offers that are genuinely competitive — real work tasks for months before operational demand is introduced.
The Dark Web Dimension:
In dark web communities, a potential source’s value is observable before any contact is made. Forum posts demonstrate technical knowledge, operational experience, access.
The community members who attract recruitment attention share a profile:
- Demonstrated technical capability mapping to operational value
- Community standing indicating knowledge is respected and likely real
- Post history revealing access, connections, specific expertise
- Visible personal characteristic suggesting motivation vector
On reputation-based forums, recruiters don’t approach members without standing. The safer position, from a recruitment resistance perspective, is actually lower profile rather than higher profile.
The most valuable-appearing targets are the most likely to be approached.
Recognition Signals — How to Identify an Approach:
Early Warning Indicators:
- Unprompted recognition — Someone contacts you to praise your specific expertise with detailed knowledge of your work
- Identity opacity — Professional identity difficult to verify independently; recent or thin profiles
- Curiosity precision — Questions mapping precisely to sensitive domains that feel too specific to be casual
- Accelerating intimacy — Relationship moves toward personal territory faster than professional norms justify
- Unexplained resource — Offers of value without apparent return interest
- Off-platform pressure — Early request to move to encrypted/less-monitored channels
- Third-country meeting — Invitation to meet where you have less protection
The LinkedIn-Specific Pattern:
LinkedIn has become the primary professional surface for state-sponsored recruitment because it provides self-disclosed targeting intelligence. Your profile is a targeting advertisement.
Profile red flags:
- Account age less than 2 years for claimed senior professional
- Low connection count for networking-active professional
- Unverifiable employers, generic descriptions
- Stock-photo appearance
- No mutual connections or only suspicious accounts
Why People Say Yes:
The primary mechanism isn’t ideology or greed — it’s the psychology of relationship and reciprocity.
A recruiter who has spent months providing genuine value — interesting conversations, professional insights, personal support — has accumulated reciprocity credit that is spent when the request arrives.
The target who says yes to the first sensitive request isn’t making an ideological decision. They’re resolving a debt.
Each small compliance creates a new reciprocity balance that makes the next compliance feel like maintenance rather than escalation.
By the time the request crosses a meaningful legal line, the target has already provided enough to feel invested in the relationship and enough to be legally exposed if disclosed.
The psychology of sunk cost compounds: having already crossed small lines, refusing to cross the next one feels inconsistent.
What To Do If You Are Approached:
- Document everything — Screenshots, dates, channel, content. Preserve before doing anything else.
- Apply the recognition framework — Score the indicators. If 40+, treat as probable approach regardless of how legitimate it feels.
- Notify your security officer — Before making further contact decisions. Not optional for scores 40+.
- If prior compliance occurred — Report immediately and voluntarily. Self-report consistently produces better outcomes than discovered compromise.
The earlier the recognition, the lower the cost of response.
Recognition at Phase 2 — when the compliment arrives and before reciprocity is established — is almost effortless.
Recognition at Phase 5 — after months of cultivation, financial exchange, incremental disclosure — is difficult, costly, potentially legally complex.
The fundamental asymmetry:
The recruiter understands the technique they’re using. The target typically doesn’t.
Professional intelligence recruitment works not because targets are naive or disloyal but because the techniques are calibrated to normal human psychology — the need for recognition, the tendency toward reciprocity, the difficulty of refusing small requests after accepting smaller ones.
These aren’t weaknesses. They’re normal features of human social cognition. They’re exploitable by anyone who has studied them professionally.
The counterintelligence response is to close the asymmetry through awareness: to describe the technique in sufficient detail that it becomes recognizable when it’s being applied.
The dark web dimension adds a context most CI programs don’t address: the technical community member who believes anonymity protects them from recruitment attention, who consequently applies less skepticism to approaches within that context than they would to a LinkedIn connection request.
Anonymity protects identity. It doesn’t protect against the psychological sequence of recognition, cultivation, and incremental commitment.
The forum member who is told they are the most capable analyst in the community has received the same operational investment as the government official who receives a dinner invitation from a think tank researcher with a thin LinkedIn profile.
The opening move is identical.
The question is whether they recognize it.
If you believe you have been approached or targeted as part of a foreign intelligence recruitment attempt — via LinkedIn, dark web, encrypted messaging, email, or in person — report it immediately to your organizational security officer or national counterintelligence service. Romania: SRI — www.sri.ro USA: FBI — tips.fbi.gov UK: MI5 — www.mi5.gov.uk DE: BfV — www.verfassungsschutz.de NL: AIVD — www.aivd.nl
Reporting is not evidence of guilt. It is evidence of integrity.