Modern security is often nothing more than a fragile passcode core, wrapped in a hard biometric shell.

1. Introduction: The Hidden Assumption
Every day, we mindlessly glance at our phones or press a finger against a sensor. Face ID and Touch ID authenticate us in a heartbeat, feeling almost like magic.
But behind this sophisticated biometric shield lies a primitive master key: a simple 6-digit passcode. How many of us are truly aware of its absolute power?
This structure isn’t unique to smartphones. Banking apps, corporate VPNs, cloud management consoles, and digital ID foundations — most of our modern systems still rely on a single, aging assumption:
“Something You Know = Who You Are”
In an era where AI can learn human thought patterns and optimize behavioral predictions in milliseconds, this foundation is quietly collapsing.
2. The Data: The Mathematical Limits of 19.9-Bit Entropy
For the readers of Data Driven Investor, numbers tell the real story. A 6-digit passcode (000000–999999) offers exactly one million combinations. In information theory, this translates to roughly 19.9 bits of entropy.
From a security standpoint, this is staggering in its weakness. For comparison:

- Modern Session Tokens: Often 128 bits or higher.
- Standard Encryption Keys (AES): 256 bits.
- 6-Digit Passcode: 19.9 bits.
Compared to modern cryptographic standards, a passcode is not just weaker; it is in a different, much lower league.
■ The Reality of Brute Force
In terms of pure computing power, testing one million combinations is trivial. While devices have rate-limiting and lockout mechanisms, these are merely “time-buying” tactics. They do nothing to stop shoulder surfing, social engineering, or malicious fallback exploitation.

■ AI-Optimized Guessing
Furthermore, AI excels at learning human preferences. PINs are not distributed uniformly; “123456,” birthdays, and repetitive patterns are overrepresented. AI can prioritize these “human-centric” numbers, reducing the practical search space to a fraction of the theoretical million.
Potential for iPhone eKYC Hacking: How “Passcode Shouldering,” “Selfies,” and a Few…
3. The Truth Behind Passcodes: A Compromise for UX
Why does such a weak mechanism remain at the heart of our systems? The answer is clear: it’s not about security; it’s about Availability.
The passcode is, by design, a fallback — a way to ensure the user is never locked out when biometrics fail. For years, tech giants have accepted a dangerous trade-off:
Reducing assurance levels to maintain high availability.
In the pre-AI era, this was a rational UX decision. In the AI era, it has become a structural liability.
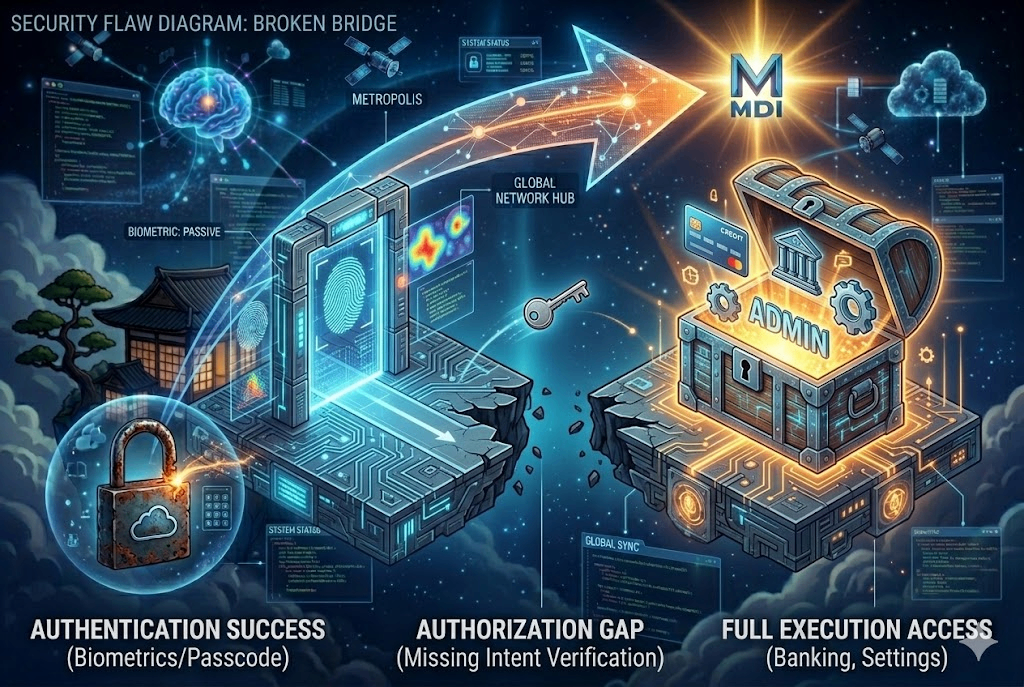
4. The Structural Flaw: The Authorization Gap
This brings us to the core concept I advocate: the Authorization Gap. Most modern OS architectures operate on the following logic:
- Authentication: Successful.
- Execution: Granted.
But there is a missing link between these two: Intent Verification. The moment a passcode fallback succeeds, the system assumes “Identity” and grants unconditional authority. It never pauses to ask:
“Why is this specific action being taken right now?”
Whether it’s a wire transfer of $50,000 or a change to your primary security settings, the system treats the “success” of a 6-digit entry as a blank check. This void is the Authorization Gap.
The $25M Deepfake: When Successful Authentication Becomes the New Single Point of Failure
5. Shell and Core: The Fragile Truth of Security
Modern security architecture currently follows this dual-layered model:
- The Outer Layer: Strong Biometrics (The Hard Shell)
- The Inner Layer: 6-Digit Passcode (The Fragile Core)
No matter how impenetrable the shell appears, as long as the “fallback” exists as a bypass, the total security of the system eventually regresses to the level of the core.
Modern security is biometrics wrapped around a passcode core.
This isn’t just a flaw in one company’s product; it is the fundamental limit of “Knowledge-based security.”
6. Acceleration in the Age of AI
In the past, exploiting this structure required significant manual effort — observation, pattern analysis, and social manipulation. AI automates and accelerates all of this.
From behavioral prediction to authority-cloning via deepfake audio, attacks have shifted from “breaking the lock” to “manipulating the human.” When the final line of defense is a 6-digit number, this shift is catastrophic.
7. The Proposal: Intent Lock
The solution is not “stronger” authentication. We need a redesign of Authorization. We must move toward a system where:
- Execution authority is constrained based on the method of authentication.
- High-risk operations refuse to accept a passcode-only fallback.
- The UI context (what the user sees) is structurally bound to the execution request.
Concept Implementation (Pseudo-code)
func executeHighRiskAction(action: Action, method: AuthMethod) {
// For high-risk operations (e.g., transfers, ID changes)
if action.riskLevel == .high {
// Reject fallback methods that lack strong intent proof
guard method == .biometricStrong else {
throw SecurityError.insufficientIntentLevel(
"Critical actions require biometric-level intent verification."
)
}
}
process(action)
}The goal is to shift the focus from “Who are you? (Identity)” to “What are you trying to do? (Intent).” This is the essence of the Intent Lock.
8. Conclusion: Refactoring Trust
Passcodes can no longer serve as the foundation of trust. They are a legacy of a pre-AI world, and they have become the Single Point of Failure for our digital lives.
We do not need more layers of authentication; we need to refactor the structure of trust itself. The next evolution of security must be the transition from Identity Verification to Intent Confinement.
Let us ensure that “successful authentication” does not become our greatest risk. It is time to rebuild trust for the AI era.
Continuing the Architectural Investigation
The Authorization Gap represents a systemic challenge that extends beyond any single platform or organization.
As part of an ongoing forensic and architectural research effort, I am documenting real-world cases and proposing structural approaches toward Intent Confinement and trust redesign.
Further Reading — Collaborative Research Series
A Proposal to Apple — Part 6: Collective Technical Audit
Beyond the Limits of One Individual: An Invitation to a Collective Technical Audit
A Proposal to Apple Part6 — Collaboration Edition
About the Author

Consultation & Project Inquiries:
👉 Request a Structural Audit / Inquiry Form
Ryu360 is a System Architect and Digital Forensics Specialist pioneering the field of Adversarial Architecture Review.
He specializes in uncovering structural vulnerabilities within “formally correct” systems — specifically the Authorization Gap in digital identity, biometrics, and eKYC frameworks. Through forensic log analysis, he identifies “unnatural silences” where system design inadvertently assists in its own sabotage, enabling attackers to bypass high-assurance security through semantic manipulation.
Ryu360 advises organizations on transitioning from simple identity verification to high-assurance Intent Lock models to neutralize AI-driven logic mapping attacks.
Expertise & Services:
- Adversarial Architecture Audits: Identifying hidden design risks in mobile and financial ecosystems.
- Forensic Investigation: Deep-dive analysis of security anomalies and “structural destruction” traces.
- Strategic Security Design: Blueprints for Intent-based Authorization and Signed Camera Feeds.
Is a 6-Digit Passcode Still Enough to Protect Everything in the AI Era? was originally published in DataDrivenInvestor on Medium, where people are continuing the conversation by highlighting and responding to this story.


