

Why do we need security compliance automations?
Automating your security compliance will mean different things depending on who you speak to. For me, and for the context of this blog post I define security compliance automations as “Software tools that can reduce the repetitive tasks for engineering, infrastructure, security, product, and legal teams in attaining security compliance”.
Audit Automations vs Control Automations
At a glance, the distinction between audit and control automations might seem subtle, but understanding their core functionalities is crucial for any technical professional working in the realm of security compliance.
Why do we need them both ? Audit Independence. This is a concept that internal audit teams are familiar with which ensures that people/tools operating a process and the ones that check that process are independent
Audit automation tools primarily focus on assessing and verifying if specific control requirements are fulfilled.
They are instrumental in preparing detailed audit reports, highlighting areas of adherence or discrepancies. For instance, such a tool would validate if the Service Level Agreement (SLA) for addressing each vulnerability has been met within the stipulated time frame. On the other hand, control automation operates on the front lines, actively enforcing or implementing security measures to meet these requirements. It’s the system that takes proactive action, such as deploying automated patches for known vulnerabilities. So, while audit automation ensures that we are aware of our compliance status, control automation ensures that we are actively compliant.

Designing your compliance with an automation-first approach
Okay, so now you know the difference between control automations and audit automations. Here are the things you can do if you are building a new security or compliance function (treat this like a checklist):
Understand context and scope: Having an understanding of your infrastructure (cloud or on-premises), the application stack and the blast radius for your organization is key to start defining your security or compliance program. This will help you pick the right tools . Your approach would differ if you are a mid-size SaaS company primarily relying on AWS vs a legacy finance company that is running Linux hosts in a data center(lab series on the latter).
Security teams come in various shapes and sizes. Depending on the business, the security team might belong to engineering or legal teams or could be a separate entity reporting to the CEO. This impacts the functioning of the security program in multiple ways, we will focus on the impact in the compliance program
If the compliance function sits within engineering, the team may have supportive peers to help with getting things (mostly with infrastructure controls) done, especially around compliance tooling. Since the broader group reports to the Head of Engineering (title may wary), there is enough incentive to get things rolling fast. It gets harder if the compliance/security sits with legal, since there is less incentive for software and product engineers to support compliance. Compliance is then seen as “yet another thing to do” that is not directly contributing to the feature set and revenue.
Identify Stakeholders: Meet with people that are affected by things you do. Understand why they don’t want you to do the things. Are they engineering teams that are expected to operate and own the security control ? or are they decision makers within the business? These are the people who would want to help first with your tooling. Reducing engineering toil with automated tooling should be a priority.
Build a culture: Traditional security teams wouldn’t want to automate things. People don’t like the idea of python scripts replacing their jobs. You need to create a culture with a narrative that automated tools do the boring and mundane work (e.g.: validating evidences) so that the security and compliance teams can focus on the changing landscape of privacy and security regulations. These automated tools act like swords, you still need someone to operate them and are better than fighting with bare hands
Understanding the underlying technology (infrastructure)

My writing will focus significantly on infrastructure since compliance programs focus on having things on the infrastructure configured securely. Compliance certification (PCI, ISO27001, SOC2, SOX) requirements are generic and may have different reporting requirements, however, having a secure infrastructure is a common theme across all certifications. Moreover, the size and complexity of the their technology stack tells a good story of their maturity and pace at which they like to operate.
Lets look at two companies;
1) Company A : A small-stage Business-to-Business Software as a Service (B2B) SaaS company has recently achieved SOC 2 certification. The company runs its application primarily on Amazon Web Services, using a relatively simple cloud architecture.
The company’s goal is to maintain security and compliance while scaling revenue and engineering velocity ahead of its Series B funding round.
Infrastructure
The product stack is intentionally simple enough to secure effectively.
Typical architecture would look like:
Users
|
Load Balancer (AWS App LB)
|
EC2 Application Servers
|
Managed Database
|
S3 Storage
The analytics pipeline pulls aggregated product data from the database for internal reporting.
To keep risk manageable, the company relies on a small number of critical SaaS platforms. The goal is to avoid SaaS sprawl, which can overwhelm a small security team.
Security Priorities
The team focuses on four manageable domains.
Identity & Access Management

Control access to:
- AWS accounts
- production systems
- SaaS tools
- developer repositories
Focus areas:
- SSO enforcement
- MFA everywhere
- role-based access
Cloud Security

Protect the AWS environment by monitoring:
- IAM privilege changes
- EC2 configuration
- S3 access policies
- network security groups
This reduces the risk of cloud misconfigurations.
Security Monitoring
Centralized logging is implemented so the team can detect incidents quickly.
Primary logs monitored would include:
- AWS activity logs
- authentication events
- system logs from EC2 instances
- application access logs
Alerts are triaged by the Security Operations Engineer (title may vary).
Compliance & Audit Readiness
The GRC analyst manages:
- SOC2 control evidence
- security questionnaires
- third-party risk reviews
- policy updates
Automation is used where possible to reduce manual work.
Security Tooling
A small security team typically maintains a focused stack rather than dozens of tools. The objective is operational simplicity and automation.
2) Company B :A publicly traded enterprise that generates over $20B in annual revenue and employs 20,000+ people globally.
This company operates several independent lines of business, including:
- digital platforms
- enterprise services
- customer products
- internal financial services
- data analytics operations
Because the company grew over decades, much of its technology stack was built internally and runs inside company-owned data centers.
Over the past decade the company has gradually adopted hybrid cloud infrastructure, primarily using Amazon Web Services and Microsoft Azure for scalable workloads. Despite its size, the company operates under public market financial discipline, meaning budgets are large but scrutinized heavily.
Organizational Structure
Technology operations are distributed across multiple business units, each running its own engineering and infrastructure teams.
Typical structure:
Units: Corporate IT, Platform Engineering, Data & Analytics, Product Engineering, Infrastructure Operations.
Because these units evolved independently, the environment contains multiple technology standards and legacy systems.
Infrastructure Model
The company operates three main infrastructure environments.
Enterprise Data Centers
Most mission-critical systems still run in company-owned facilities.
Infrastructure includes:
- large virtualization clusters
- internal storage networks
- enterprise databases
- custom orchestration platforms
The company also maintains internal tooling for provisioning and monitoring infrastructure.
Hybrid Cloud Environments
Over the last decade, certain workloads have moved to cloud environments.
Common cloud workloads:
- web front-end applications
- data analytics
- burst compute workloads
- development environments
Cloud providers include:
- Amazon Web Services
- Microsoft Azure
These environments are integrated with internal networks through private connectivity and identity federation.
Legacy Systems
Some business-critical systems remain on older enterprise platforms, including:
- legacy financial systems
- long-running customer databases
- proprietary operational platforms
These systems often require specialized expertise to maintain.
Security Organization
Unlike startups, the company maintains dedicated teams across the entire security lifecycle.
Approximate security staffing: 80–120 professionals.
Core groups include:
Security Engineering, Security Operations, Cloud Security, Application Security, GRC, Internal Audit.
Even with this staffing, the organization constantly competes for budget and organizational support.
Compliance Environment
Because the company is publicly traded, it must comply with multiple regulatory frameworks.
Typical obligations include:
- SOX financial controls
- ISO 27001 information security management
- regional data protection laws
- contractual enterprise security requirements
Compliance oversight involves coordination between:
- GRC teams
- internal audit
- legal counsel
- business unit leadership
Security Challenges
Despite significant resources, the company faces systemic security challenges.
Infrastructure Fragmentation
Because systems evolved over decades:
- multiple monitoring tools exist
- inconsistent security controls appear across environments
- different business units operate differently
Legacy Risk
Older systems may:
- lack modern security features
- require outdated software dependencies
- be difficult to patch or replace
Hybrid Visibility Gaps
Monitoring must cover:
- on-premise data centers
- hybrid cloud environments
- internal corporate networks
Achieving unified visibility across these environments is difficult.
Organizational Complexity
Security initiatives often require cooperation from:
- infrastructure teams
- product engineering teams
- business unit leadership
Projects can stall due to political and operational friction.
Security Tooling Environment
The enterprise operates a large but structured tool ecosystem.
Key categories include:
FunctionCapabilityIdentity managementEnterprise directory servicesSecurity monitoringSIEM and SOC toolingEndpoint securityEnterprise EDRNetwork protectionIDS/IPS platformsCloud monitoringCloud security posture toolsVulnerability managementEnterprise scanning platforms
Security teams must integrate cloud telemetry, on-prem logs, and application activity into centralized monitoring.
Strategic Security Priorities
Security leadership typically focuses on four long-term initiatives.
Hybrid Security Architecture
Create unified security controls across:
- data centers
- cloud environments
- internal corporate networks
Identity Modernization
Centralize authentication and authorization across the enterprise.
Security Automation
Reduce manual compliance and monitoring processes through automation.
Risk Reduction in Legacy Systems
Gradually modernize or isolate older platforms that present security risks.
Operational Reality
Even with significant resources, the security organization constantly balances:
- regulatory compliance
- operational stability
- budget limitations
- competing business priorities
Security programs therefore evolve incrementally, rather than through rapid transformation.
Compliance certification requirements will be interpreted differently for both companies. One will be a lot more challenging to operate and automate for audits. These are two extremes so your organization would sit somewhere in-between the two examples.
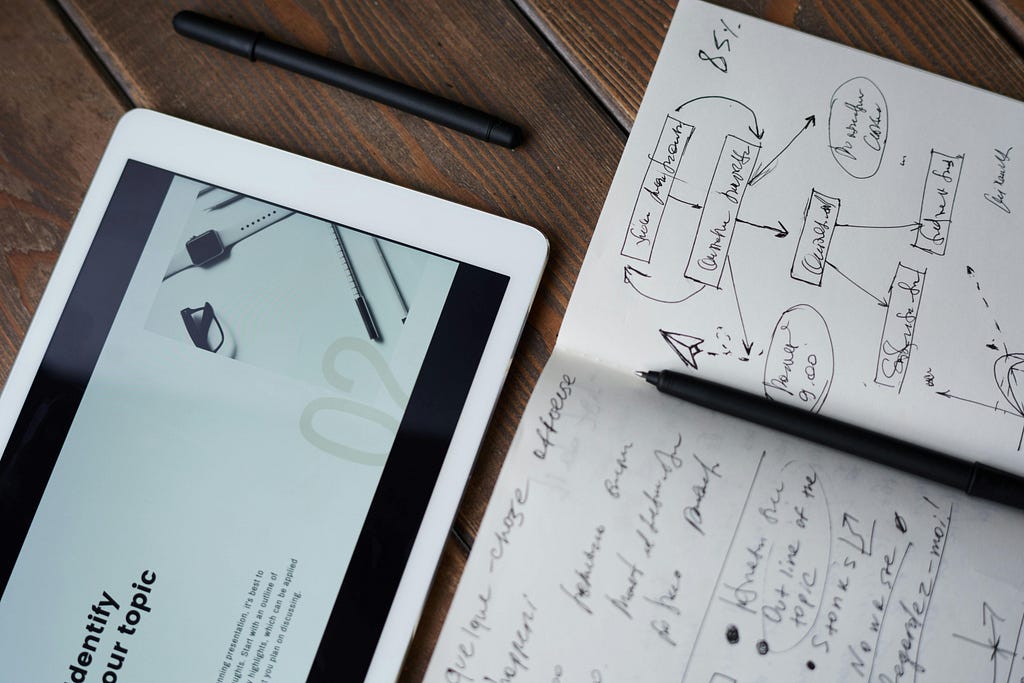
Below is a scribbled diagram of the company size, infrastructure style and how complex would it be to automate their compliance audits.

Even thought it is complicated, such organizations should consider automating their audits due to the incredible return on investment it offers.
Vendor tool selection
If you are Company A., you can simply pick any of compliance automation tools(we will do that in a future blog) and you can achieve automation for 75–80% of your painful controls, open source tools would provide a lot of value here.
If you are Company B, you should be setting aside resources to build a GRC Engineering Team to help you build these tools. They will start with one control one certification, and work their way through solving the scaling problem.
If you are somewhere in the middle (most companies out there). You may not get the support for building a dedicated team that does the development of tools. You can possibly get a vendor tool for some of the controls and automate them with accuracy and completeness. For the controls that require integrations with custom tooling, you can write simple python scripts that run off your laptop. If you use Google Sheets and your auditors enjoy spreadsheet-like evidences, you can use the Apps Scripts to pull auditable data. Once you have multiple such scripts that have time-and-again proved that scripts have saved time, reduced human error, you can asked for a dedicated headcount for developing more such automations. Proving that your scripts have been useful for compliance testing is important to get buy-in from leadership.

Architecture for enterprise-grade GRC Automation tool
Conclusion
Automation is not about replacing compliance teams; it is about scaling their effectiveness. Whether you operate a lean SaaS startup or a complex enterprise with decades of infrastructure, the core challenge remains the same: proving that security controls exist and work consistently.
An automation-first mindset reduces repetitive evidence collection, minimizes human error, and frees teams to focus on real risk management instead of manual reporting. Start small, automate one control, one audit requirement, or one workflow. Over time, these incremental improvements compound into a resilient compliance program where security, engineering, and audit teams collaborate through systems rather than spreadsheets.
In the next article, I will tackle one of the use cases, expand on it, tools and hopefully design and implement an automation lab.
I hope I provided value in this piece. I hope you have found value in today’s article. Consider clapping, subscribing and following me on my socials. If you need to reach me , I am a DM away.
- LinkedIn: https://www.linkedin.com/in/m49d4ch3lly
- Twitter: https://twitter.com/m49D4ch3lly
- GitHub: https://github.com/UFarouk10
- Gmail: [email protected]
GRC Engineering Series: Let’s Design an Automated Compliance System was originally published in Coinmonks on Medium, where people are continuing the conversation by highlighting and responding to this story.



